Connecting to IBM Security Verify Access
The EmpowerID IBM Security Verify Access connector allows organization to manage user identities and access permissions in IBM Security Verify Access from within EmpowerID. The setup involves creating an account store in the EmpowerID Identity Warehouse and configuring it to synchronize identity data.
Procedure
Step 1 – Create an IBM Security Verify Access account store
-
On the navbar, expand Admin > Applications and Directories and select Account Stores and Systems.
-
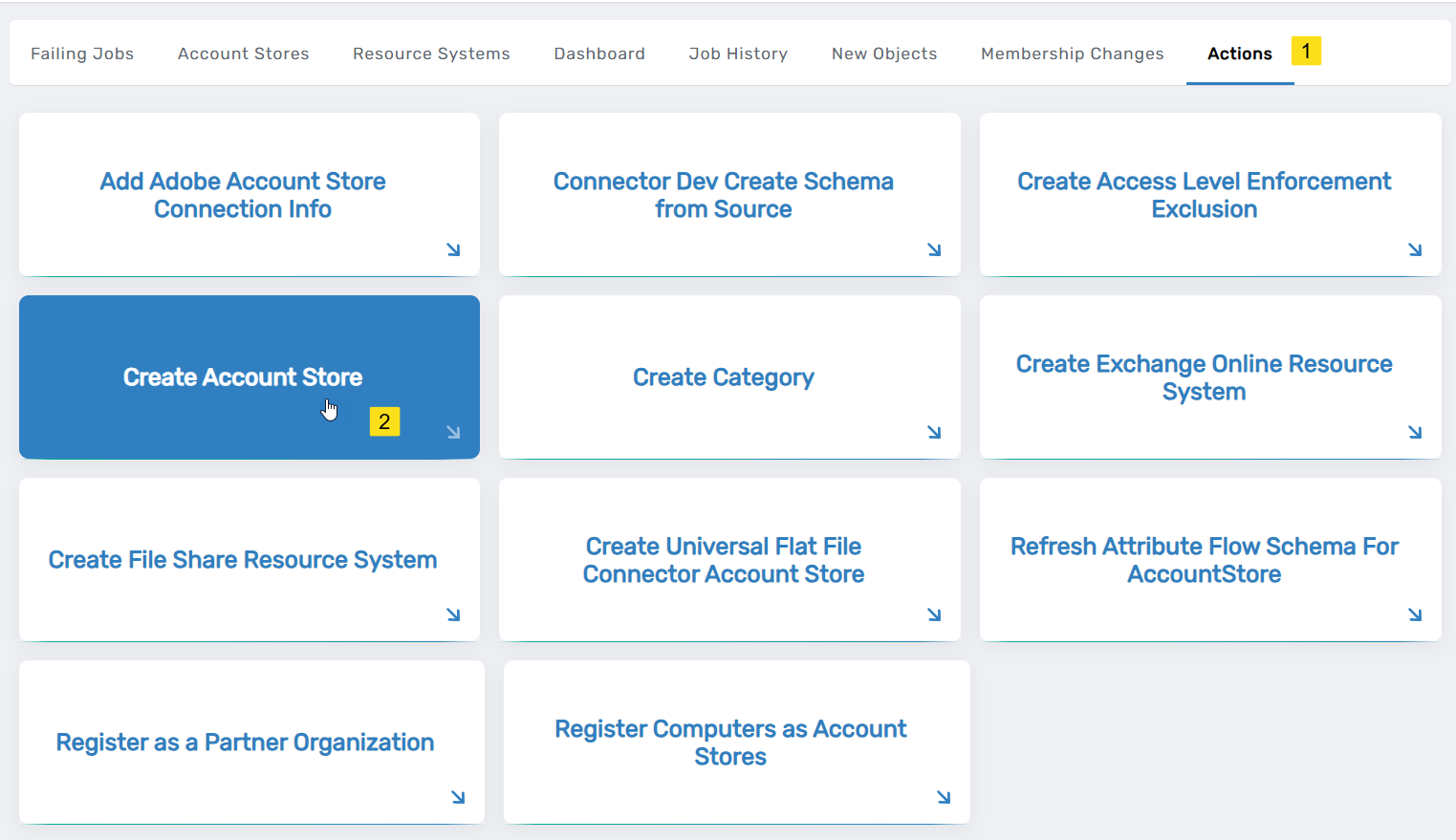
On the Account Stores page, select the Actions tab and then click Create Account Store.
-
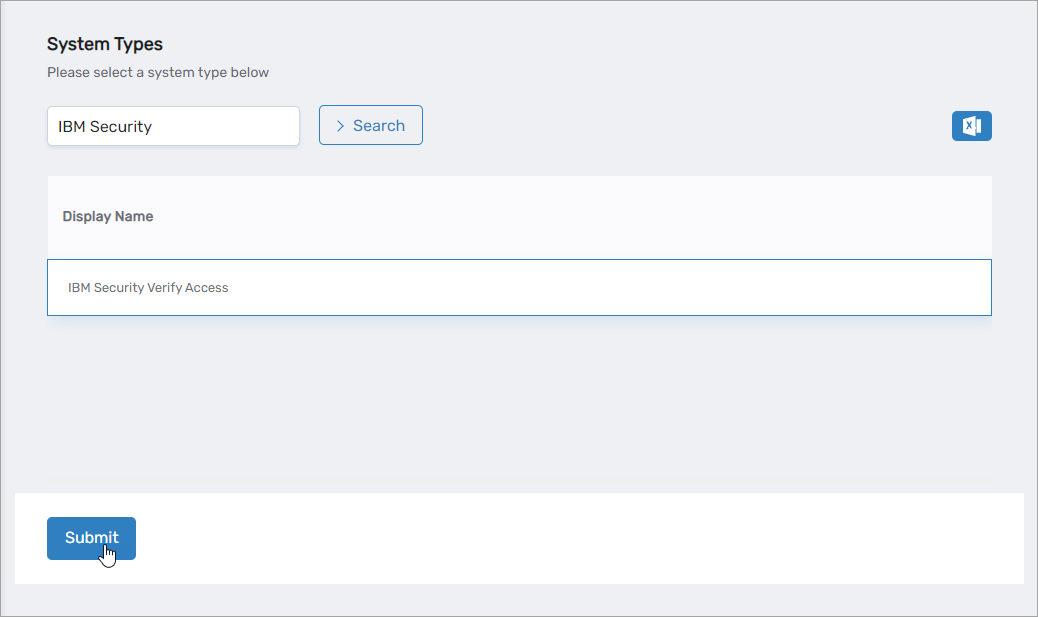
Under System Types, search for IBM Security.
-
Click the IBM Security Verify Access record to select the type and then click Submit.
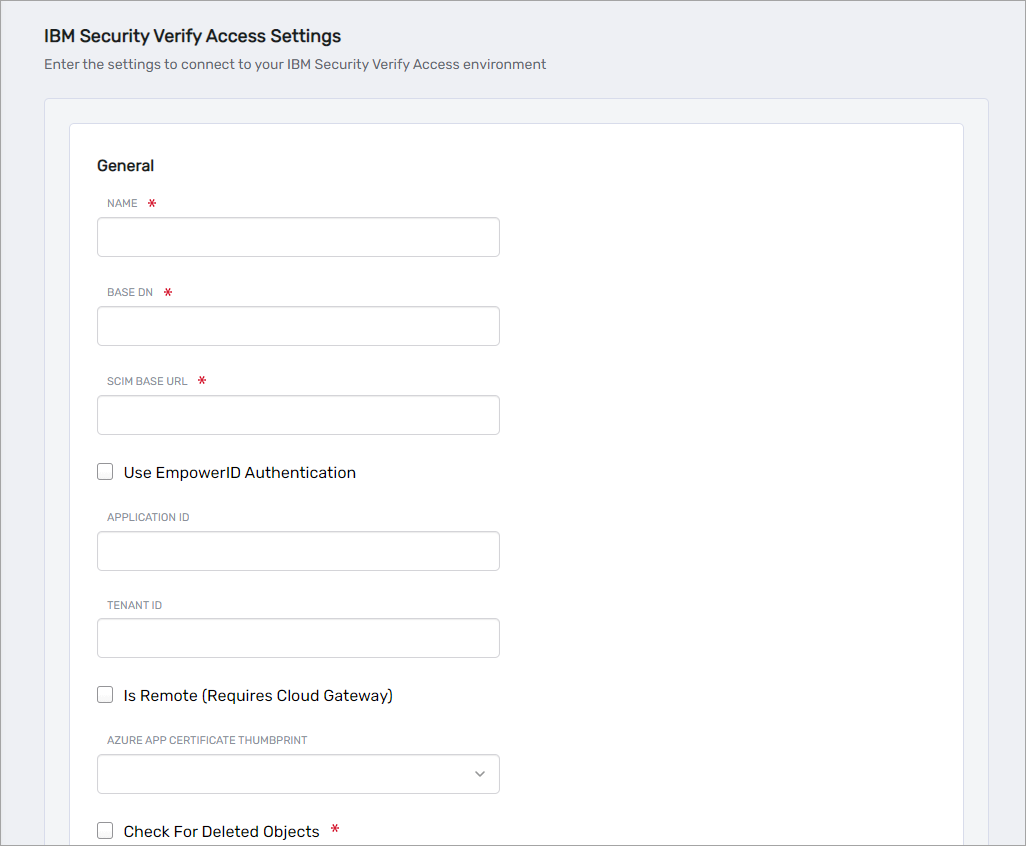
This opens the IBM Security Verify Access Settings form, which is where you enter information that allows EmpowerID to connect to the system.
-
On the IBM Security Verify Access Settings form, fill in the following information according to your authentication scenario:
Using EmpowerID for Authentication
Use this option when hosting the microservice outside of Azure.
- Name - Enter a name for your account store.
- Base DN - Enter the root OU of the LDAP system, such as
dc=example,dc=com. - SCIM Base URL - Enter the URL for the SCIM app service. The base URL should include the version and look similar to the following:
http://192.168.87.106:8080/empoweridisam/scim/v2/ - Use EmpowerID Authentication - Select this option when using EmpowerID for authentication.
- OAuth Application GUID - Enter the GUID of the OAuth application you created for IBM Security Verify Access in EmpowerID.
- URL For Access Token - Enter the URL to your EmpowerID environment, such as
https://sso.empoweriam.com, wheresso.empoweriam.comis the FQDN of your EmpowerID front-end server. - Is Remote (Requires Cloud Gateway) - This setting appears for account stores with local directories, such as Active Directory, LDAP, SAP, etc. When enabled, this tells EmpowerID to use the Cloud Gateway Connection for that account store. The Cloud Gateway Connection must be installed on an on-premise machine. For installation information, please see Installing the EmpowerID Cloud Gateway Client.
- Check For Deleted Objects - Select this option to sync deleted objects. If this is not set to true, the connector will not disable deleted objects.
- Check For Deleted Objects Interval Minutes - Specify the interval in minutes that EmpowerID should check for deleted objects.
Using EntraID for Authentication
Use this option when hosting the microservice in Azure.
- Name - Enter a name for your account store.
- Base DN - Enter the root OU of the LDAP system, such as
dc=example,dc=com. - SCIM Base URL - Enter the URL for the SCIM app service. The base URL should include the version and look similar to the following:
http://192.168.87.106:8080/empoweridisam/scim/v2/ - Application ID - Enter the Client ID of the service principal application you registered in Azure for EmpowerID.
- Tenant ID - Enter the Tenant ID for your Azure tenant hosting the app service.
- Is Remote (Requires Cloud Gateway) - This setting appears for account stores with local directories, such as Active Directory, LDAP, SAP, etc. When enabled, this tells EmpowerID to use the Cloud Gateway Connection for that account store. The Cloud Gateway Connection must be installed on an on-premise machine. For installation information, please see Installing the EmpowerID Cloud Gateway Client.
- Azure App Certificate Thumbprint - Enter the thumbprint of the certificate you uploaded to Azure for the service principal application.
- Check For Deleted Objects - Select this option to sync deleted objects. If this is not set to true, the connector will not disable deleted objects.
- Check For Deleted Objects Interval Minutes - Specify the interval in minutes that EmpowerID should check for deleted objects.
EmpowerID creates the account store and the associated resource system. The next step is to verify the resource system parameters.
Step 2 – Verify Resource System Configuration Parameters
-
On the navbar, expand Admin > Applications and Directories and select Account Stores and Systems.
-
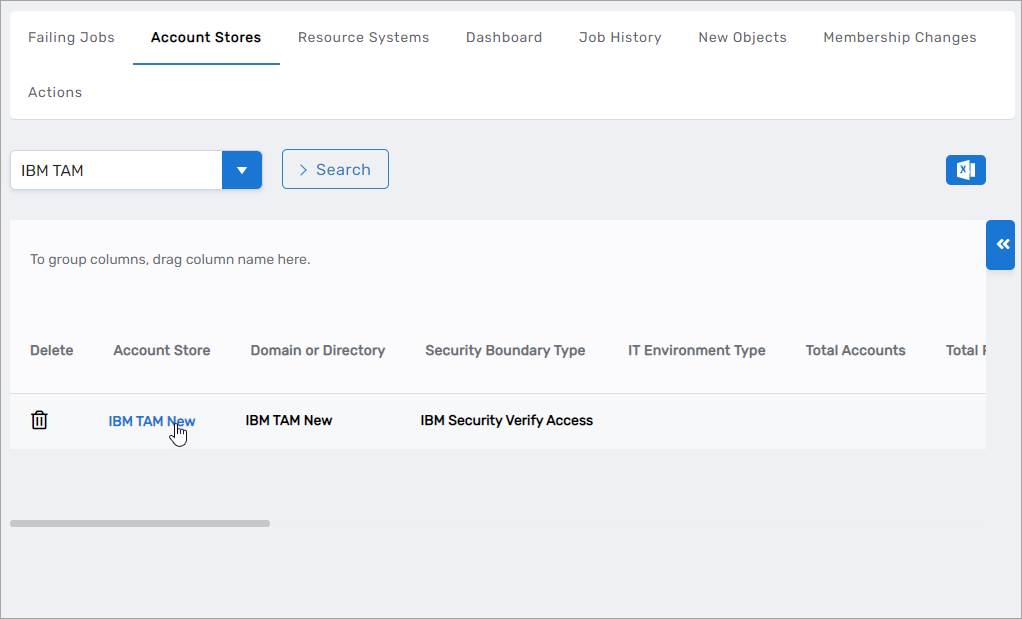
On the Find Account Store page, select the Account Stores tab and search for the IBM Security Verify Access account store you just created.
-
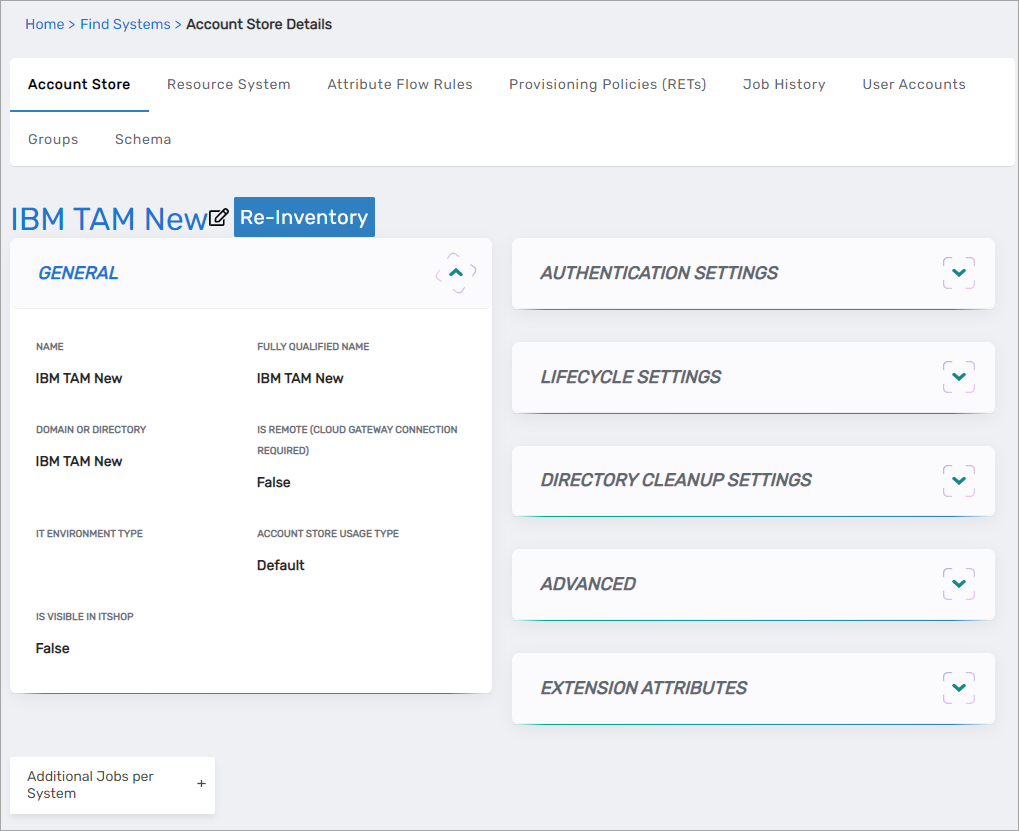
Click the Account Store link for the account store.
This directs you to the Account Store and Resource System page for the account store. This page contains several tabs related to the account store that you can access to view and manage the account store and resource system.
-
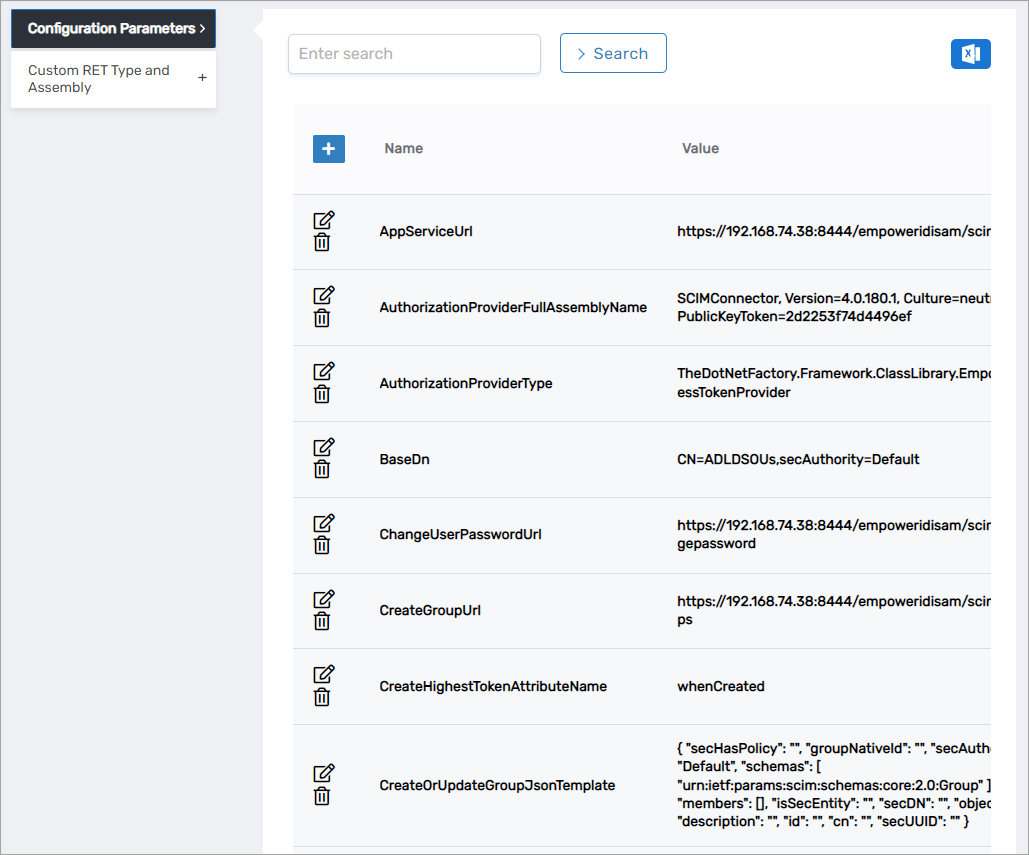
Select the Resource System tab and then expand the Configuration Parameters accordion on the page.
-
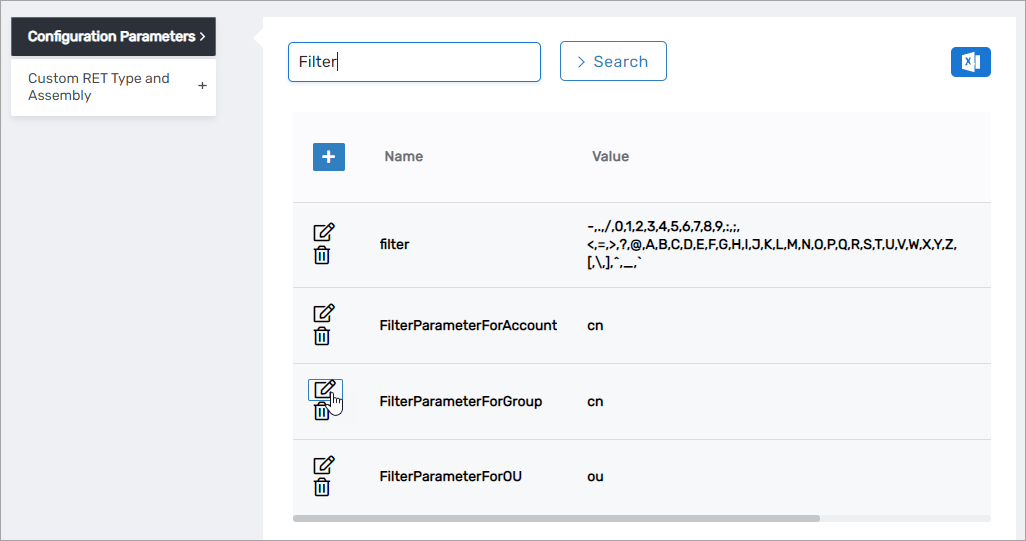
Verify the following parameters are correct for your system:
cautionPlease note that the values for
ApplicationIDandTenantIDare encrypted and that you will not see the values in the user interface.Configuration ParametersName Value Description AppServiceUrl {Your Base SCIM Url}URL for the SCIM app service, including the version. AuthorizationProviderFullAssemblyName SCIMConnector, Version=4.0.180.1, Culture=neutral, PublicKeyToken=2d2253f74d4496efProvider assembly to retrieve EmpowerID token. AuthorizationProviderType TheDotNetFactory.Framework.ClassLibrary.EmpowerIDAccessTokenProviderProvider type to retrieve EmpowerID token. BaseDn dc=ibm,dc=comThe base distinguished name of LDAP. ChangeUserPasswordUrl {Your Base SCIM Url}changepasswordURL to change a user password. CreateGroupUrl {Your Base SCIM Url}groupsURL to create a group. CreateHighestTokenAttributeName createTimestampAttribute used for incremental inventory. CreateOrUpdateGroupJsonTemplate (JSON Template) JSON template for creating or updating groups. CreateOrUpdateOUJsonTemplate (JSON Template) JSON template for creating or updating organizational units. CreateOrUpdateUserJsonTemplate (JSON Template) JSON template for creating or updating users. CreateOUUrl {Your Base SCIM Url}ouURL to create an organizational unit. CreateUserUrl {Your Base SCIM Url}usersURL to create a user. DateTimeCulture en-USDateTime format used by the connector. DeleteBatchSize 1000Number of objects processed per call during deletions. DeleteGroupJsonTemplate (JSON Template) JSON template for deleting groups. DeleteUserJsonTemplate (JSON Template) JSON template for deleting users. FilterParameterForAccount uidLDAP attribute used to retrieve users. FilterParameterForGroup cnLDAP attribute used to retrieve groups. FilterParameterForOU ouLDAP attribute used to retrieve organizational units. GetAllActiveObjectsUrl {Your Base SCIM Url}entityURL to retrieve all active objects. ModifyHighestTokenAttributeName modifyTimestampAttribute for incremental inventory updates. NameFormat {0}/FirstNameDefines how names are constructed. OAuthProviderApplicationID {Your Oauth Application ID}OAuth Client ID for authentication. PageSize 500Number of objects returned per inventory call. ResetUserPasswordUrl {Your Base SCIM Url}resetpasswordURL to reset a user's password. RunFullInventoryAfterXRuns 20Frequency of full inventory runs. UrlForAccessToken {Url}URL to retrieve an access token. -
To edit the value of a parameter, click the Edit button for the parameter you want edit.
- Enter the new value in the Value field and click Save.
- Repeat as needed.
The next step is to configure attribute flow.
Step 3 – Configure Attribute Flow
- From the Account Stores tab of the Account Stores and Systems page, search for the account store you just created and click the Account Store link for it.
- Click the Attribute Flow Rules tab to view the current rules for the account store. Please note that the attributes available depend on the account store.
- To change the flow for an attribute, click the Attribute Flow drop-down located between the Person Attribute column and the External Directory Attribute column, and select the desired flow direction from the context menu.
- To change the score for any of the available CRUD operations (Create, Update and Delete), enter the new score in the appropriate field. By default, scores are weighted evenly, which means that a change to an attribute originating in one connected external directory has the same authority as a change to an attribute occurring in another connected external directory.
EmpowerID only considers scores for attribute CRUD operations when multiple account stores with the same user records are connected to EmpowerID, such as would be the case if an HR System and this account store were being inventoried by EmpowerID.
Now that the attribute flow has been set, you can configure the mapping between the SCIM microservice attribute and the EmpowerID account/group/OU table attribute if needed.
Step 4 – Schema Mapping (Optional)
- On the navbar, expand Admin > Applications and Directories and select Manage Schema.
- Select the Security Boundary Object Attributes tab and search for user as Object Type ID and IBMTAMScim as Security Boundary Type.
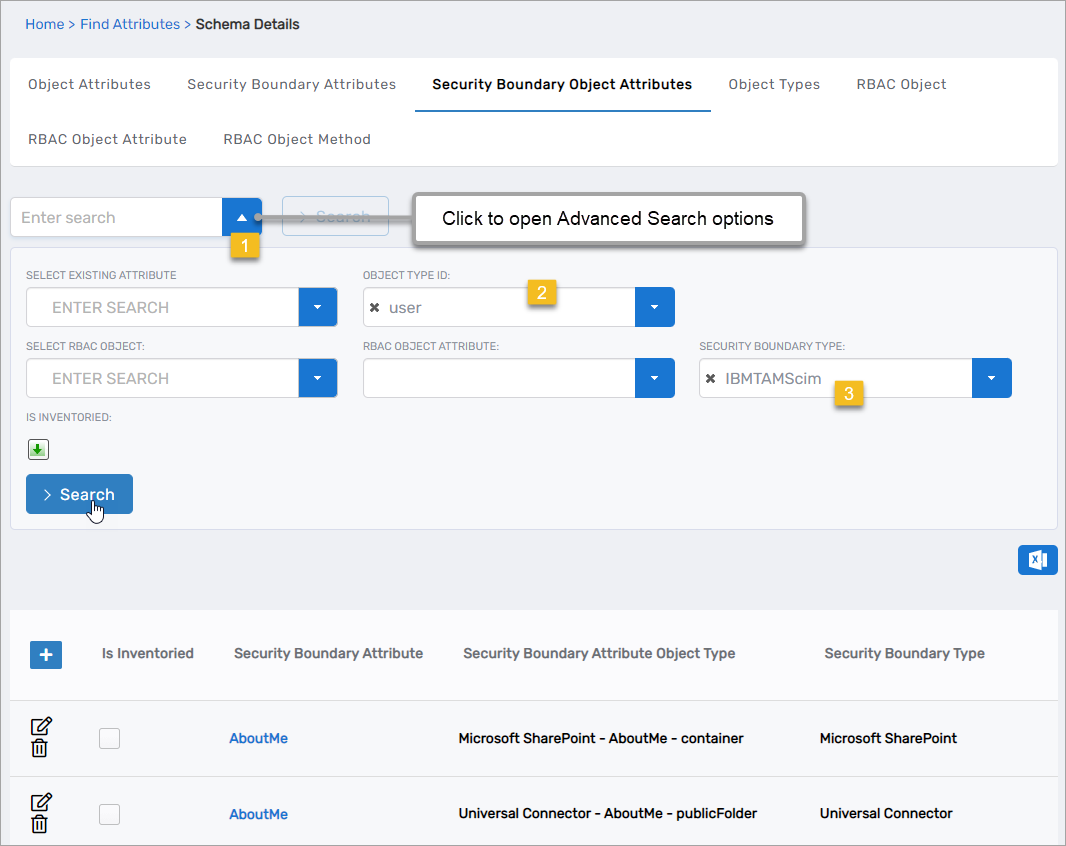
- Click the Edit button beside the Security Boundary Object Attribute you want to modify.
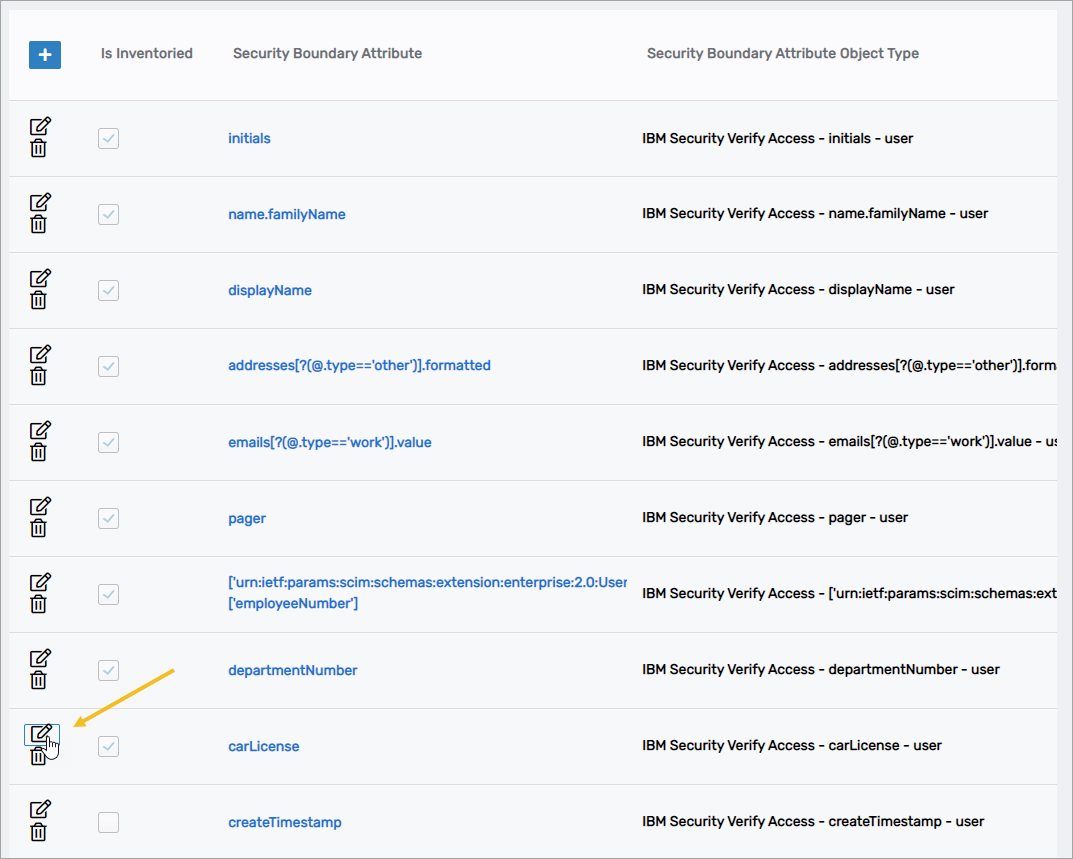
- Change the RBACObject Attribute you want to use in the mapping and save your change.
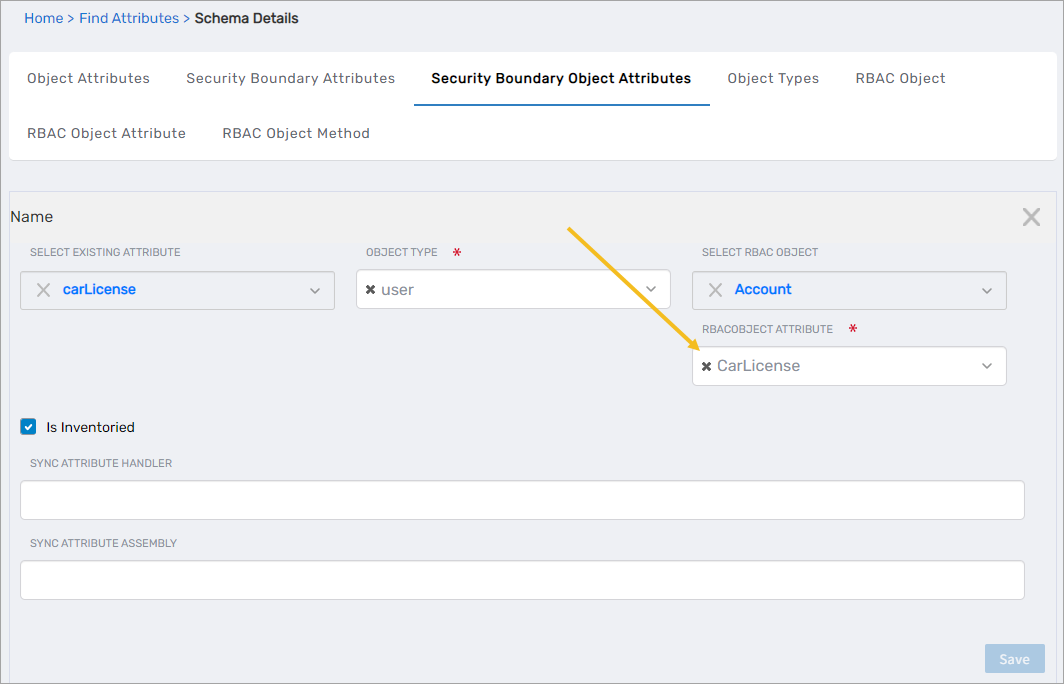
- Repeat for each mapping you want to change.
Step 4 – Configure account store settings
-
On the Account Store and Resource System page, select the Account Store tab and then click the pencil icon to put the account store in edit mode.
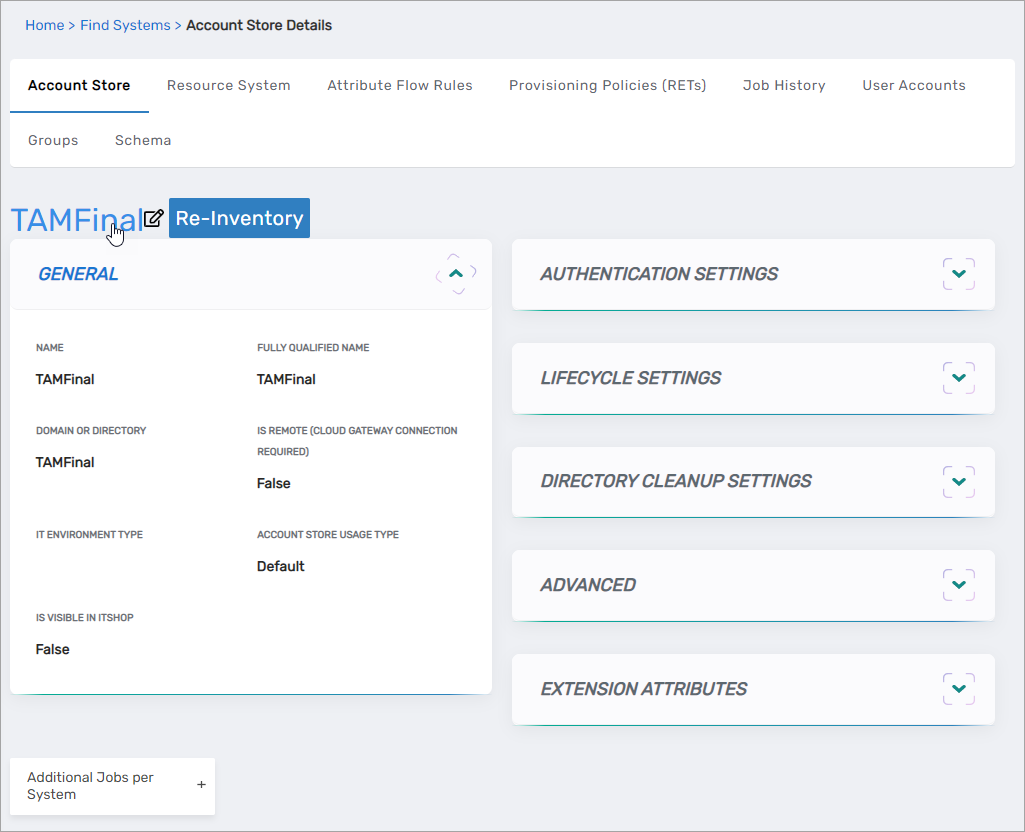
This opens the edit page for the account store. This page allows you to specify the account proxy used to connect EmpowerID to your IBM Security Verify Access system as well as how you want EmpowerID to handle the user information it discovers during inventory. Settings that can be edited are described in the table below the image.
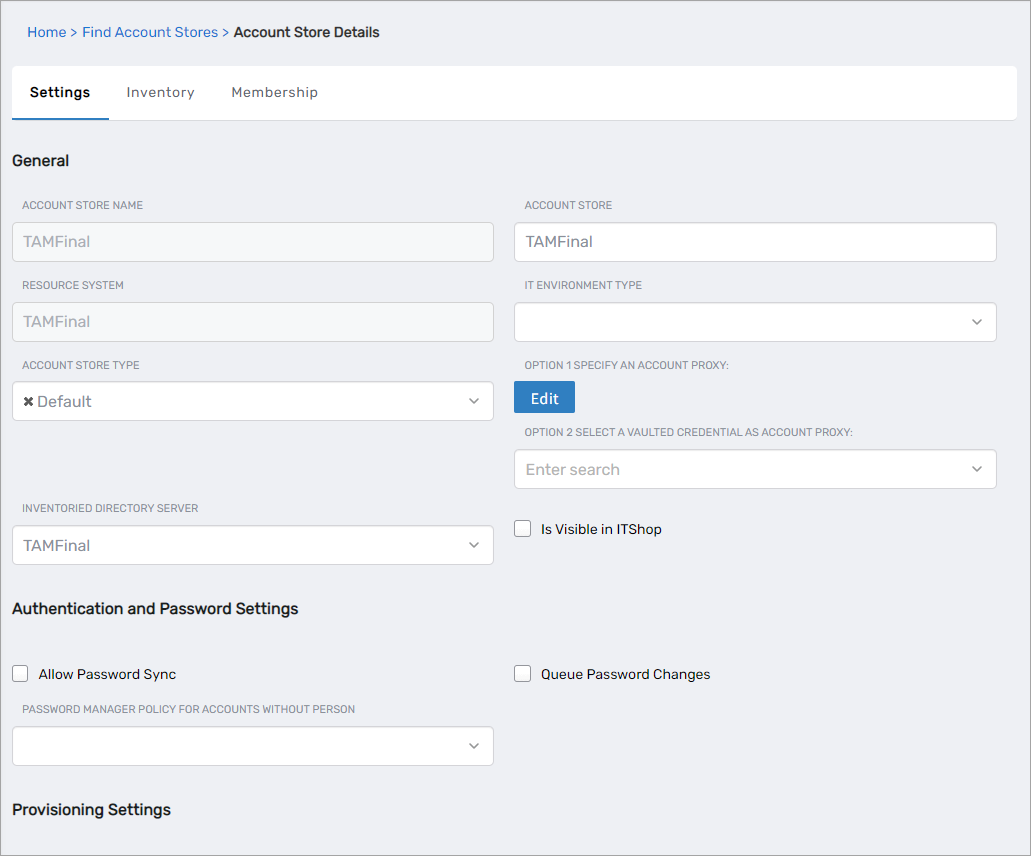
Account Store Settings Setting Description General Settings IT Environment Type Allows you to specify the type of environment in which you are creating the account store. Account Store Type Allows you to specify the type of account store you are creating. Option 1 Specify an Account Proxy Allows you to change the credentials for the account that EmpowerID uses to connect to and manage the account store. Option 2 Select a Vaulted Credential as Account Proxy Allows you to use a credential that you have vaulted in EmpowerID as the account that EmpowerID uses to connect to and manage the account store. Inventoried Directory Server Allows you to select a connected server as the directory server for the account store. Is Remote (Cloud Gateway Connection Required) This setting appears for account stores with local directories, such as Active Directory, LDAP, SAP, etc. When enabled, this tells EmpowerID to use the Cloud Gateway Connection for that account store. The Cloud Gateway Connection must be installed on an on-premise machine. For installation information, please see Installing the EmpowerID Cloud Gateway Client. Is Visible in IAM Shop Specifies whether the account store can be used to filter objects relative to the account store, such as groups, to users searching for resources in the IAM Shop. Authentication and Password Settings Allow Password Sync Enables or disables the synchronization of password changes to user accounts in the domain based on password changes for the owning person object or another account owned by the person. This setting does not prevent password changes by users running the reset user account password workflows. Queue Password Changes Specifies whether EmpowerID sends password changes to the Account Password Reset Inbox for batch processing. Password Manager Policy for Accounts without Person Specifies the Password Manager Policy to be used for user accounts not joined to an EmpowerID Person. Provisioning Settings Allow Person Provisioning (Joiner Source) Specifies whether EmpowerID Persons can be provisioned from user accounts in the account store. Allow Attribute Flow Specifies whether attribute changes should flow between EmpowerID and the account store. Allow Provisioning (By RET) Allows or disallows the Resource Entitlement (RET) Inbox process to auto-provision accounts for this domain for users who receive RET policy-assigned user accounts, but have not yet had them provisioned. Allow Deprovisioning (By RET) Allows or disallows the Resource Entitlement Inbox process to auto de-provision accounts for this domain for users who still have RET policy-assigned user accounts, but no longer receive a policy that grants them a user account in the domain. De-provisioning only occurs if the de-provision action on the Resource Entitlement policy is set to De-Provision. Max Accounts per Person This specifies the maximum number of user accounts from this domain that an EmpowerID Person can have linked to them. This prevents the possibility of a runaway error caused by a wrongly configured Join rule. It is recommended that this value be set to 1 unless users will have more than 1 account and you wish them to be joined to the same person. Business Role Settings Allow Business Role and Location Re-Evaluation Specifies whether Business Role and Location re-evaluation should occur for the account store Business Role and Location Re-Evaluation Order Specifies the order of the account store for re-evaluating Business Roles and locations Inventory Auto Provision OUs as IT System Locations Specifies whether EmpowerID should automatically provision external OUs as IT System locations Inventory Auto Provision External Roles as Business Roles Specifies whether EmpowerID should provision Business roles for external account store roles Default Person Business Role Specifies the default EmpowerID Business Role to be assigned to each EmpowerID Person provisioned from the user accounts in the account store. Default Person Location (leave blank to use account container) Specifies the default EmpowerID Location to be assigned to each EmpowerID Person provisioned from the user accounts in the account store. Group Settings Allow Account Creation on Membership Request Specifies whether EmpowerID creates user accounts in the account store when an EmpowerID Person without one requests membership within a group belonging to the account store. Recertify External Group Changes as Detected Specifies whether detected group changes should trigger recertification. SetGroup of Groups to Monitor for Real-Time Recertification Specifies the SetGroup or Query-Based Collection with groups that need to be recertified when changes to the membership of one or more of those groups occurs. The setting must be set to the GUID of the target SetGroup. If the GUID for a specific SetGroup is not set and Recertify External Group Changes as Detected is enabled for the account store, EmpowerID processes all security group memberships for recertification.
Group recertification is processed by the Continuous Group Membership Recertification permanent workflow. This workflow must be enabled for recertification to occur.Directory Clean Up Enabled Directory Clean Up Enabled Specifies whether the SubmitAccountTermination permanent workflow should claim the account store for processing account terminations. When enabled, accounts in the account store that meet the qualifications to be marked for deletion are moved into a special OU within the external directory, disabled and finally deleted after going through an automated approval process. This process involves setting a number of system settings in EmpowerID and requires multiple approvals by designated personnel before an account is finally removed from the account store. Report Only Mode (No Changes) When enabled, a report of what the Directory Clean Up process would do is written to the log. The process itself is ignored and all accounts are set to Termination Pending, Special Use Settings Automatically Join Account to a Person on Inventory (Skip Account Inbox) Specifies whether EmpowerID should attempt to join user accounts in the account store to an existing EmpowerID Person during the inventory process. When enabled, the Account Inbox is bypassed. Automatically Create a Person on Inventory (Skip Account Inbox) Specifies whether EmpowerID should create new EmpowerID Persons from the user accounts discovered in the account store during the inventory process. When enabled, the Account Inbox is bypassed. Queue Password Changes on Failure Specifies whether EmpowerID should send password changes to the Account Password Reset Inbox only when the change fails. Inventory Settings Inventory Schedule Interval Specifies the time span that occurs before EmpowerID performs a complete inventory of the account store. The default value is 10 minutes. Inventory Enabled Allows EmpowerID to inventory the user information in the account store. Membership Settings Membership Schedule Interval Specifies the time span in minutes that occurs before EmpowerID runs the Group Membership Reconciliation job. The default value is 10 minutes. Enable Group Membership Reconciliation Allows EmpowerID to manage the membership of the account store’s groups, adding and removing user to and from groups based on policy-based assignment rules. -
Edit the account store as needed and then click Save to save your changes.